If you’re an IT auditor or security analyst and you don’t know how to ping a server, then I have some words for you:
LEARN HOW!
So let’s do it.
I’m assuming most of my readers already know how to do this. If so, please answer the poll question at the bottom. If not, please read on, then answer the poll question. Thanks!
Why Ping?
You can use the ping command for a number of reasons, but for this post, I’m going to focus on just these two reasons: 1) determine whether a server (or PC or network device, such as a router) is up and running, and 2) determine the IP address of a device if you have its name.
How to ping
In Windows, to ping a device, you must open the command prompt. In most Windows operating systems, just click Start, Run, type cmd and press Enter. Since my computer account is ITauditSecurity, I get this prompt:
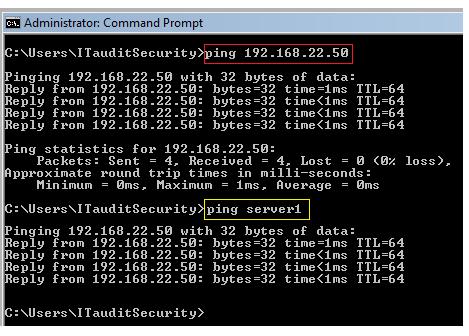
You can either ping a device by IP address or name (this post deals with version 4 IP addresses; version 6 is different; today, most IP addresses are still version 4 and will probably be that way for several more years).
If the server has an IP address of 192.168.22.50 and the server’s name is server1, you can ping it by IP address (see highlight in red box below) or name (white box) as follows.
As shown in the second example above, if you know the server’s name, you can ping it to learn it’s IP address. For example, if you have an IP address range that is subject to a firewall rule, you can ping the device to see whether its IP address is in the range affected by that rule.
Can’t Ping?
If you can’t reach the device, you’ll get a message like those shown below (see green boxes).
You might receive this kind of a response due to a number of reasons–here’s just a few:
- The asset is not up and running.
- A network device is not allowing you to reach the asset due to a network problem or by design (i.e., your ping request was dropped or blocked). The asset may indeed be alive and well, but “hidden”.
- Your ping command was incorrect (wrong server name or IP address, or a command syntax error occurred).
Regardless of the reason, the important thing is that you need to ask a subject matter expert (SME) why you couldn’t reach the device. If it was not due to your own error, the reason could give you a better understanding of the network or the device you are trying to ping–which might shed light on your audit or research you are performing.
Ping a Web Site
You can also ping a web site, like google.com. Just type ping google.com and press Enter.
This is my favorite way to determine whether a computer has Internet access (if the ping is successful, it has access).
Admin Account?
My astute readers may have noticed that the first 2 images above show that the ITauditSecurity account is an administrator account (see the blue banner at the top of those images). As I have noted before on this blog, I do not use an administrator account for everyday usage and strongly suggest you don’t either (see Log in as Root or Administrator?).
I created these images on my admin account because I did not want to reveal the account name I use for my non-admin account (if your account reflects your name, you’re giving that away freely to every web site you visit). But then I logged out and blogged this post under my non-admin account.
Poll
.
Pinging a server is one of the items I listed under What IT Auditors Ought to Know – and Don’t!. If you didn’t know how to ping, check this post out to see what else you might not know.


“If you’re an IT auditor or security analyst and you don’t know how to ping a server, then I have some words for you…”
I’d have some words for a security analyst who doesn’t know how to ping – and they wouldn’t be “learn how”… :-) It would be more along the lines of “GTFO”…
LikeLike
Richard,
Of course I’m being nice. But I’ve met some analysts like that, no joke.
Your last name adds a funny chuckle to our discussion….
Thanks for your comment!
LikeLike
What you should have shed light upon are the various replies possible and their explanation (not only destination unreachable). Also you are suppose to change you admin account name to something else to be more secure because as it is there is a route to you. Thanks.
LikeLike
Wo,
Changing your admin account doesn’t affect pings, but changing the name of that account is never a bad idea, as it helps detect and prevent attacks that use the default account name. You can always configure your firewall to reject pings, but more importantly, the other ports are still open. You’d want to stealth those ports more so than the port that allow ping replies.
What I tried to address in the above post is how to tell if a server or device is up during an audit. Typically, companies don’t turn off ping replies inside a company for many reasons.
In this post, I wasn’t addressing security at all.
LikeLike
i appreciate your advice
THANKS.
LikeLike
Pingback: New IT Auditors Should Start Here | ITauditSecurity
I am amazed how many hits this post gets every week. I had no idea that this topic would be that popular….PING ON!
LikeLike
Pingback: Blogging about Internal Audit (10 tips) | ITauditSecurity